As tech enthusiasts and business innovators, you know that the Internet of Things (IoT) is not just a buzzword; it's a revolutionary shift in how we interact with devices and data. But with great power comes great responsibility — ensuring seamless connectivity and managing these devices is vital. Enter AWS IoT Device Shadows, the unsung heroes of IoT device management.
Imagine having a digital twin for your IoT devices, creating a parallel universe where every update, state change, and command is mirrored and managed — enter the IoT Device Shadows.
These virtual representations ensure that your devices and applications are always on the same page, even when network connectivity decides to play hide and seek.
In this article, we'll dive deep into the nuts and bolts of IoT Device Shadows, specifically focusing on AWS's implementation.
We'll unpack what AWS IoT Device Shadows are, how they work, and why they are a game-changer for IoT deployments. We'll also guide you through the setup and management of IoT Shadows, sprinkled with best practices and pro tips to optimize your IoT adventures.
So, buckle up whether you're a seasoned CTO navigating the vast cloud seas, looking for a CTO as a service, or a startup captain steering your tech ship through IoT waters! We're about to embark on a journey through the AWS IoT Device Shadow universe, ensuring you come out on the other side with all the knowledge and tools you need to manage your IoT fleet like a pro.

We take care of serverless development so you can focus on your business
Don't want to wait for our site launch? Let's talk about your idea right now.

Understanding IoT Device Shadows
AWS IoT Device Shadow emerges as the lighthouse in the vast ocean of IoT device management, guiding your devices and applications toward seamless interaction and synchronization. But what exactly are these IoT Device Shadows, and how do they play such a pivotal role in the IoT ecosystem? Let's dive in and demystify these digital twins.
Defining IoT Device Shadows
An AWS IoT Device Shadow, in its essence, is a JSON document that acts as a virtual representation of your physical IoT device on the AWS cloud. Think of it as a digital doppelganger, mirroring the device's current state, including its attributes, metadata, and the latest reported and desired states. It's like having a cloud-based buddy for your device that knows everything about it, from what it's currently up to to what it should be doing next.
The Role in IoT Device Management
In the dynamic world of IoT, devices can be scattered across various locations, often in areas with intermittent network connectivity. Managing and communicating with these devices can be like trying to have a phone conversation in a tunnel—challenging, to say the least. This is where the IoT Shadow Device AWS comes into play.
The AWS IoT Device Shadow acts as a steadfast intermediary, ensuring that even when a device goes offline, its last known state is stored in the cloud. Applications can retrieve and set the device's state via the shadow without communicating directly with it. When the device is back online, it can synchronize its state with the shadow, ensuring consistency and reliability in device behavior and data reporting.
Device State Synchronization
Device state synchronization is akin to a dance between the device and its shadow, ensuring that both partners are in sync, regardless of the network's rhythm. When a device's state changes, it reports the new state to its shadow.
Similarly, an application can set a desired state in the shadow, which the device will retrieve and implement. This two-way communication ensures that both the device's reported state and the desired state from applications are always in harmony, even if network disruptions try to step on their toes.
The IoT Core Device Shadow plays a crucial role here, providing a buffer that absorbs the impacts of network latency and availability issues. It ensures that commands and state information are not lost in transmission but are stored securely, waiting for the device to receive and act upon them.
By using AWS IoT Device Shadows, you're not just managing devices; you're orchestrating a symphony of synchronized states and commands, ensuring that your IoT ecosystem dances to the beat of efficiency and reliability. And that, dear readers, is the magic of IoT Device Shadows in the grand performance of IoT device management.
Kyrylo Kozak
CEO, Co-founderGet your project estimation!

IoT Management Techniques Overview
Navigating the seas of IoT device management requires a solid grasp of the various techniques and protocols at your disposal. Each technique has its own set of functionalities and use cases. Let's explore fundamental methods you can employ to ensure smooth sailing in your IoT journey.
Direct Device Communication
Direct device communication is like a straight-up, no-nonsense, face-to-face chat with your IoT devices. In this approach, applications interact directly with the devices, sending commands and receiving data without intermediaries. While this method offers real-time interaction, it can be challenging when devices are offline or have unreliable network connections. That's where the resilience of AWS IoT Device Shadow comes in handy, ensuring that device state and commands are retained and synchronized when connectivity is restored.
MQTT
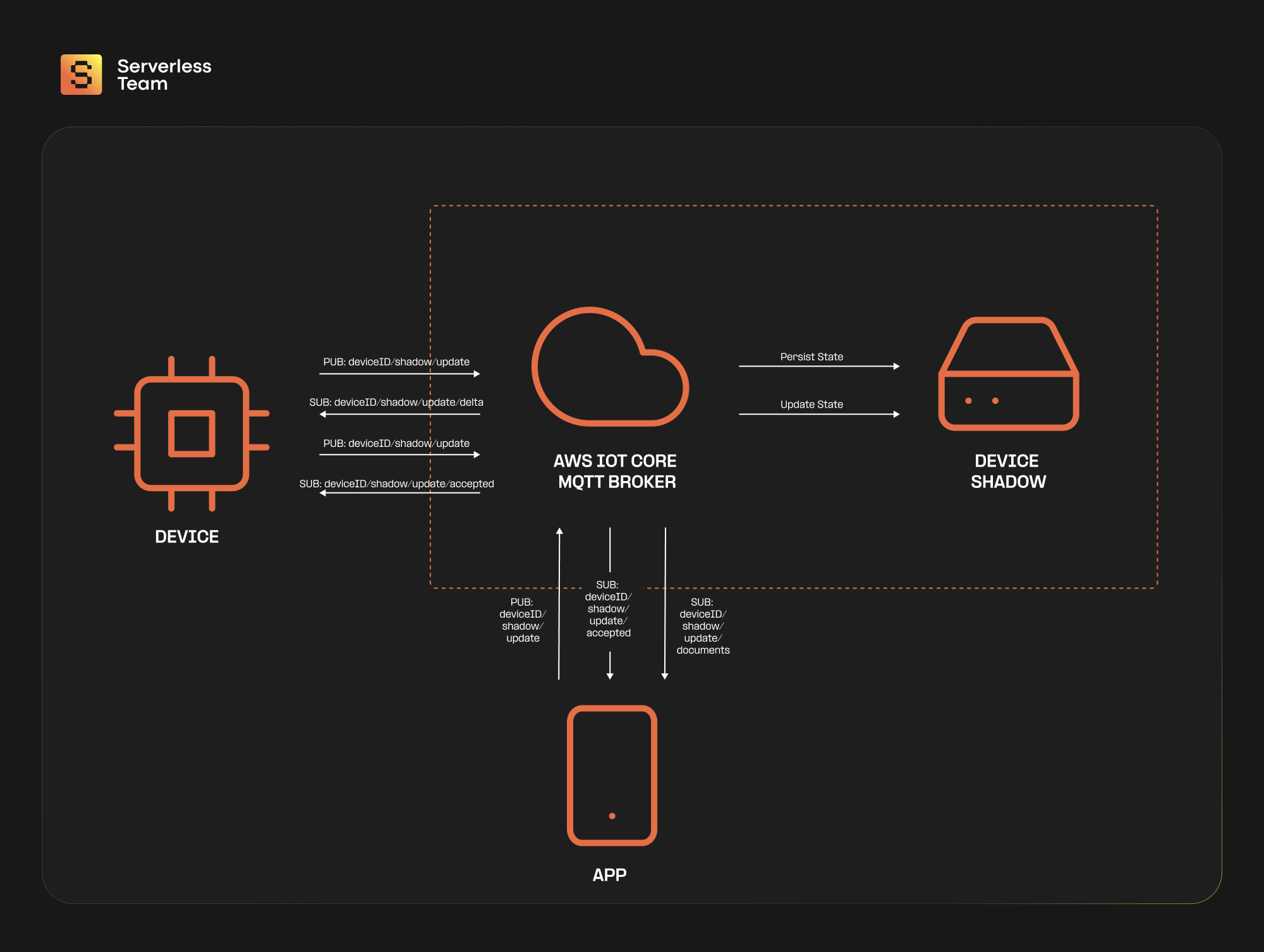
MQTT (Message Queuing Telemetry Transport) is the cool, calm, and collected communicator of the IoT world, specifically designed for low bandwidth, high latency, or unreliable networks. This publish-subscribe-based messaging protocol allows devices to send (publish) information to a server, which applications can retrieve (subscribed). By utilizing MQTT topics, Shadows ensure that the current state of the device is readily available, providing a continuous channel for interaction. This constant availability facilitates uninterrupted communication, allowing applications and services to engage with and manipulate the device's state whenever necessary, ensuring a seamless and responsive IoT ecosystem.
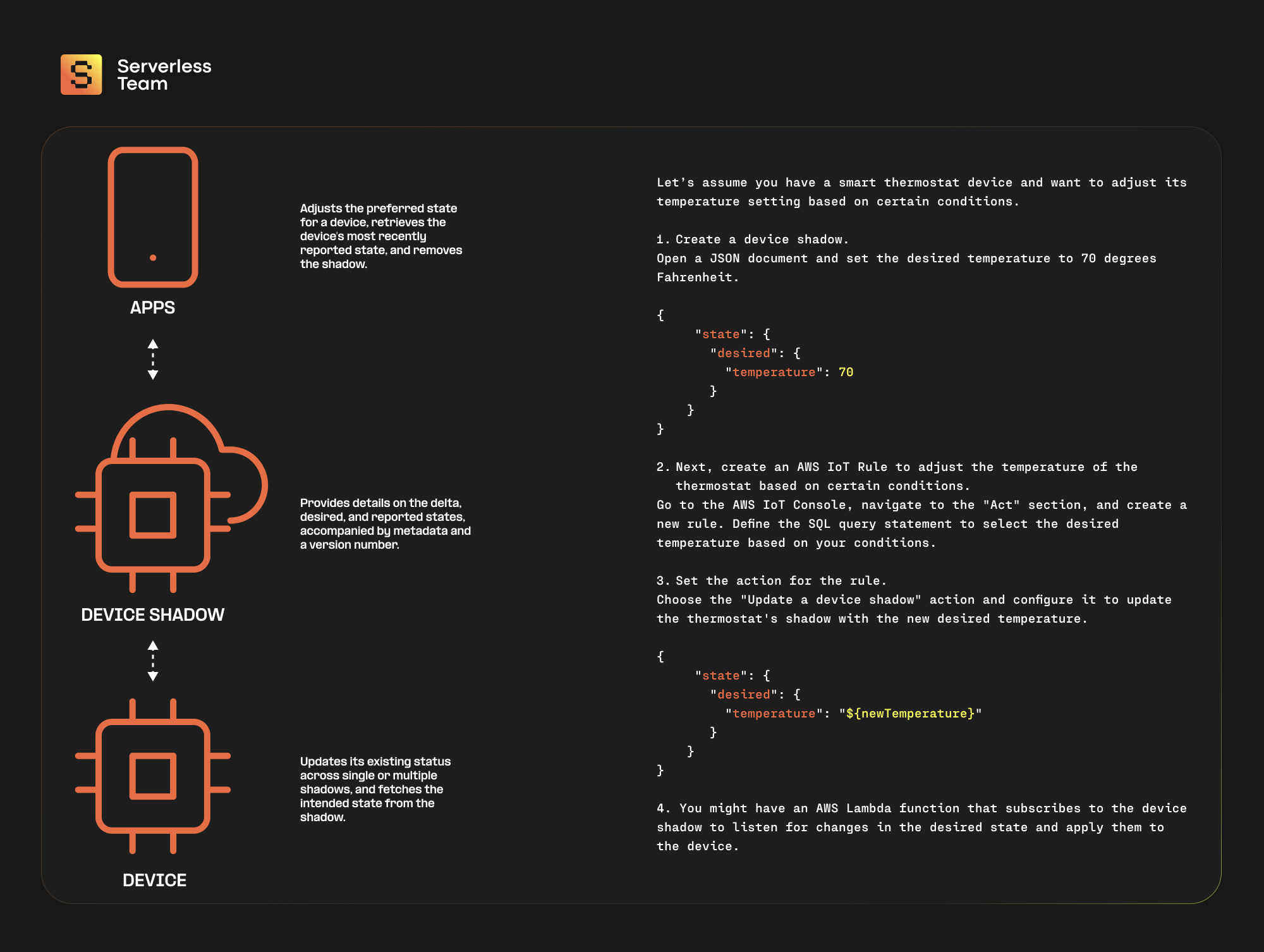
Here's a little architectural example:
CoAP
CoAP (Constrained Application Protocol) is like MQTT's lightweight cousin, explicitly designed for constrained devices operating in constrained networks. It follows a request-response model similar to HTTP but with minimal overhead, making it ideal for resource-constrained IoT devices. While CoAP can be used for direct communication between devices and applications, integrating it with the IoT Core Device Shadow ensures that state synchronization and device management are maintained efficiently, even in constrained environments.
HTTP/HTTPS
The granddad of communication protocols, HTTP/HTTPS, is also viable for IoT device management. It operates on a request-response model and is supported by virtually all internet-connected devices. While it may have a higher overhead than MQTT or CoAP, it's widely adopted and well-understood. Integrating HTTP-based communication with AWS IoT Device Shadow can provide an additional layer of reliability and state management, ensuring that your devices are always in sync, regardless of network conditions.
Device Shadows and Rules Engine
Using AWS IoT Device Shadows with the AWS IoT Rules Engine provides a powerful mechanism for managing your IoT devices. The Rules Engine allows you to define SQL-based rules that trigger actions based on device data and states. By combining this with the persistence and synchronization capabilities of IoT Core Device Shadow, you can create sophisticated device management workflows that ensure your devices behave exactly as they should, even when they're out of direct reach.
Advantages of IoT Device Shadows
Let’s delve into the treasure trove of benefits that IoT Device Shadows bring to the table, ensuring your IoT fleet is connected but also smart, secure, and ready for anything.
1. Improved Device State Management:
AWS IoT Device Shadows meticulously keeps track of device states, preferences, and last-known feelings (okay, maybe not feelings, but you get the gist). With these digital twins, you have a constant, reliable source of truth for each device’s state, accessible anytime, anywhere. This ensures that even if a device goes offline, its latest state is preserved, allowing applications to interact with the shadow instead of the device directly, leading to more reliable and consistent device management.
2. Offline Device Interaction:
In the unpredictable world of IoT, network connectivity can be as fickle as weather—sunny one moment, gone the next. IoT Shadow Device AWS shines brightly here, allowing interactions with devices to continue, rain or shine. Commands and state changes can be sent to the device's shadow, and when the device is back online, it can sync up, ensuring no command is left behind.
3. Enhanced Security:
When it comes to IoT, security is not just a feature; it's a necessity. With AWS IoT Device Shadows, security is baked into the cake. All interactions with device shadows are subject to AWS's robust security mechanisms, including authentication, authorization, and encryption. This ensures that only authorized entities can access or modify device states, keeping your IoT fleet safe from unwelcome intruders.
4. Simplified Application Development:
Developing applications for IoT can be like navigating a maze blindfolded. But with IoT Core Device Shadow, you get a map and a flashlight. Applications can interact with device shadows using well-defined APIs, abstracting away the complexity of direct device communication. This leads to cleaner, more maintainable code and allows developers to focus on building stellar applications rather than wrestling with device connectivity issues.
5. Scalability and Flexibility:
As your IoT fleet grows, managing each device individually can become tricky. AWS IoT Device Shadows provide a scalable solution, ensuring that whether you have 10 devices or 10,000, each has its own shadow, and state management is handled consistently. Additionally, the flexibility of AWS's infrastructure allows you to tailor your device shadows to your specific needs, ensuring that as your IoT ecosystem evolves, your device management capabilities develop with it.
Limitations and Drawbacks of IoT Device Shadows
While AWS IoT Device Shadows offer many advantages in managing your IoT fleet, navigating this journey with both eyes open is crucial. Like any technology, IoT Device Shadows have their quirks and complexities. Let's shine a light on its potential limitations and drawbacks.
1. Added Complexity:
Integrating AWS IoT Device Shadows into your IoT architecture is akin to adding a new instrument to an orchestra. While it brings harmony and synchronization, it also introduces an additional layer of complexity. Developers must ensure proper configuration and management of the shadows, handle state synchronization correctly, and integrate the device shadows seamlessly with the rest of the system. This added complexity can sometimes lead to a steeper learning curve, especially for teams new to the AWS IoT ecosystem.
2. Potential Latency Issues:
The IoT Shadow Device AWS is a middleman between your devices and applications, ensuring that commands and state updates are preserved and synchronized. However, this intermediation can sometimes introduce latency, especially when dealing with many devices or operating in regions with less optimal AWS infrastructure. This latency can impact real-time device interactions and timely decision-making.
3. Scalability Challenges:
AWS IoT Device Shadows are designed to scale, but like any system, they have their limits. Managing and maintaining thousands of device shadows can become challenging as your IoT fleet grows. Ensuring that each shadow is updated promptly and that state synchronization scales efficiently with the number of devices requires careful planning and optimization. Overlooking these aspects could lead to scalability bottlenecks, hindering the performance and reliability of your IoT ecosystem.
4. Resource Utilization and Costs:
Each AWS IoT Device Shadow consumes resources, and with AWS, resources translate to costs. As you scale your IoT fleet and the number of device shadows grows, resource utilization can increase significantly, leading to higher costs. It's essential to optimize your use of device shadows, ensuring that they provide value and efficiency rather than becoming a costly overhead.
5. Dependency on AWS Infrastructure:
By leveraging IoT Core Device Shadow, you're closely tying your IoT device management to the AWS ecosystem. While AWS provides robustness and reliability, this dependency means any disruptions in AWS services could impact your IoT operations. It also means migrating to a different cloud provider could require significant effort and re-architecture.
So, while AWS IoT Device Shadows bring synchronization, reliability, and security to the IoT table, it’s crucial to navigate these waters with a clear understanding of the potential limitations and challenges. By acknowledging and planning for these potential drawbacks, you ensure that your IoT fleet sails smoothly, fully leveraging the power of device shadows while mitigating the potential storms of complexity, latency, scalability, and costs.
Use Cases and Scenarios of AWS IoT Device Shadows
The beauty of AWS IoT Device Shadows truly shines when applied to real-world scenarios, demonstrating their power to simplify, streamline, and secure IoT device management. Let’s explore some practical examples where IoT Shadow Device AWS plays a starring role, transforming challenges into opportunities for innovation and efficiency.
Smart Home Automation
Imagine a scenario where a smart thermostat is part of a connected home ecosystem. The thermostat is responsible for maintaining the perfect temperature, ensuring a comfortable environment for the inhabitants. With the AWS IoT Device Shadow, even when the thermostat temporarily loses connectivity, the desired temperature setting is stored in the shadow. When connectivity is restored, the thermostat synchronizes with the shadow, applying the latest settings. This ensures a consistent and comfortable home environment, no matter the network hiccups.
Industrial Equipment Monitoring
In the industrial realm, consider a fleet of machines in a manufacturing plant, each equipped with sensors and actuators. These machines must be monitored and controlled in real-time to ensure optimal performance and prevent downtime. The IoT Core Device Shadow is a resilient link between the machines and the monitoring applications. Even if a machine goes offline, its status and control commands are retained in the shadow, ensuring seamless operation and maintenance and reducing costly downtime.
Agricultural Crop Monitoring
In the agricultural sector, IoT device shadows prove invaluable for monitoring and controlling farm equipment and sensors. For example, sensors monitoring soil moisture levels can report their data to the AWS IoT Device Shadow. Even if the sensors lose connectivity due to a rural location, the data and irrigation commands are retained in the shadow. When connectivity is restored, the irrigation system can synchronize with the shadow, ensuring that crops receive the right amount of water at the right time.
Healthcare Patient Monitoring
In healthcare, patient monitoring devices are critical for tracking vital signs and ensuring patient safety. With IoT Shadow Device AWS, patient data, and device states are continuously synchronized to the cloud, ensuring that healthcare providers have access to the latest patient information, even if a particular device goes offline. This provides continuous patient care and timely medical intervention when needed.
5. Fleet Management and Logistics:
Consider a fleet of delivery trucks, each equipped with IoT devices for tracking location, fuel efficiency, and cargo conditions. The IoT Core Device Shadow ensures that even when a truck enters an area with poor connectivity, its status and location information are retained in the shadow. Logistics managers can send route updates and instructions to the shadows, which the trucks will receive and implement once connectivity is restored, ensuring efficient fleet management and timely deliveries.
AWS IoT Device Shadows are invaluable assets in each of these scenarios, ensuring that device states are managed consistently, commands are retained and applied, and data is synchronized, regardless of network connectivity. Whether creating a comfortable home, streamlining industrial operations, nurturing crops, safeguarding patient health, or managing a fleet of trucks, IoT Device Shadows are pivotal in enhancing efficiency, reliability, and innovation.
Comparing IoT Management Techniques
Navigating the world of IoT device management is akin to choosing the right tool for a job—each technique has its strengths and weaknesses. Let’s dive into a comparison of AWS IoT Device Shadows with other common IoT management methods, shedding light on when it's the star of the show and when another method might steal the spotlight.
AWS IoT Device Shadows
Strengths:
- Reliability: IoT Device Shadows maintain each device's persistent, reliable state, ensuring data integrity even when devices go offline.
- Synchronization: Automatic synchronization of device state when restored connectivity keeps devices and applications in harmony.
- Security: Leveraging AWS's robust security mechanisms, Device Shadows ensure that only authorized entities can access or modify device states.
- Scalability: AWS infrastructure provides a scalable solution that grows with your IoT ecosystem.
Weaknesses:
- Complexity: Device Shadows can increase system complexity by introducing an additional layer of abstraction.
- Latency: Intermediation between devices and applications may introduce latency, potentially impacting real-time interactions.
- Cost: As a paid AWS service, extensive use of Device Shadows can lead to increased costs.
Use Device Shadows for scenarios requiring reliable state management, offline device interaction, and secure, scalable solutions. They are particularly beneficial for fleets of devices where consistent state synchronization is crucial.
Direct Device Communication
Strengths:
- Real-Time Interaction: Direct device interaction ensures minimal latency, ideal for real-time applications.
- Simplicity: Without an intermediary, the system architecture can be more straightforward.
- Cost-Efficiency: Eliminating the need for a cloud service could result in cost savings.
Weaknesses:
- Reliability: Without a persistent state, data may be lost if a device goes offline.
- Scalability: Directly managing a large fleet of devices can become cumbersome and less efficient.
- Security: Ensuring secure direct communication with each device can be challenging.
Direct device communication is ideal for real-time, simple applications with reliable device connectivity, and the system architecture can handle direct interactions.
MQTT (Message Queuing Telemetry Transport)
Strengths:
- Lightweight Protocol: Designed for low-bandwidth, high-latency conditions, making it well-suited for IoT devices.
- Bi-Directional Communication: Supports both publish and subscribe models, enabling two-way communication between devices and applications.
- Quality of Service Levels: Offers different levels of message delivery assurance.
Weaknesses:
- Broker Dependency: Requires a broker to manage communications, which could be a single point of failure.
- Limited Security: While it supports TLS/SSL, additional security measures need to be implemented at the application level.
- Lack of State Persistence: Does not inherently provide a persistent device state.
MQTT is a strong choice for lightweight, bi-directional communication in bandwidth-constrained environments, mainly when real-time updates are essential.
CoAP (Constrained Application Protocol)
Strengths:
- Designed for Constrained Devices: Ideal for low-power, low-resource devices.
- RESTful Design: Simplifies integration with web technologies.
- Low Overhead: Minimal protocol overhead makes it efficient for constrained networks.
Weaknesses:
- Limited Security: While it supports DTLS, additional security considerations are needed.
- Less Mature: Not as widely adopted as other protocols, leading to potential interoperability issues.
- No State Management: Like MQTT, it lacks inherent state persistence.
CoAP is well-suited for resource-constrained devices in environments where a lightweight, RESTful protocol is beneficial.
While AWS IoT Device Shadows offers a robust, secure, and scalable solution for IoT device management, the best choice depends on your specific requirements. For scenarios demanding reliable state management and seamless offline interactions, IoT Device Shadows are a stellar choice. For simpler, real-time applications, direct device communication, MQTT, or CoAP might be the way to go.
Understanding the strengths and weaknesses of each method ensures that you choose the right tool for your IoT adventure, ensuring a smooth journey and a successful outcome.
Considerations for Implementation
Let's dive into some practical advice to ensure a smooth sailing implementation and efficient management of your IoT shadows.
Getting Started with AWS IoT Device Shadows:
- Familiarize Yourself: Before diving in, ensure you have a solid understanding of AWS IoT Device Shadows, how they work, and the benefits they bring.
- Set Up an AWS Account: If you don’t have one already, create an AWS account to access the IoT Core services.
- Define Your Devices: Clearly define the devices in your IoT ecosystem, outlining their roles, capabilities, and the data they will be interacting with.
- Create and Configure Device Shadows: Use the AWS IoT Console to create and configure device shadows for your defined devices. Ensure that each shadow accurately represents the device it’s associated with.
Critical Considerations for IoT Architecture Design:
- Scalability: Design your architecture with scalability in mind. As your device fleet grows, your use of device shadows and related resources can scale accordingly.
- Security: Prioritize security in your design. Utilize AWS’s security features to ensure that only authorized entities can access or modify your IoT shadows and associated devices.
- Reliability: Consider the reliability of device connections and design your system to handle intermittent connectivity gracefully, leveraging device shadows to maintain device state and command continuity.
- Synchronization: Plan for efficient state synchronization between your devices and their associated shadows, ensuring data consistency and integrity.
Best Practices for Managing IoT Device Shadows:
- Keep Shadows Synchronized: Regularly update device shadows to ensure they accurately reflect the current and desired future state of the devices they represent.
- Optimize Resource Usage: Be mindful of resource utilization and associated costs. Optimize device shadows to ensure they provide value without becoming a costly overhead.
- Handle Conflicts Gracefully: Implement conflict resolution strategies to handle scenarios where the device and shadow states may diverge, ensuring data consistency.
- Monitor and Audit: Regularly monitor and audit your device shadows and associated IoT devices, ensuring everything functions as expected and identifying any areas for optimization.
- Leverage AWS Features: Take full advantage of the features and tools provided by AWS IoT Core Device Shadow to enhance your device management, including versioning, desired and reported state management, and update timestamps.
- Plan for Disaster Recovery: Have a robust backup and disaster recovery plan to handle potential issues, ensuring that your IoT ecosystem can recover gracefully from disruptions.
By carefully considering these aspects and following best practices, you ensure a successful implementation of IoT Device Shadows, unlocking a world of efficiency, reliability, and innovation in your IoT projects. If you want a deeper analysis, drop our team a line, and our experts will help you in no time.
Is IoT Device Shadows Right for You?
After sailing through the seas of IoT Device Shadows, it's time to drop anchor and reflect: Is this the right technology to chart your course in the vast IoT ocean? Let’s recap the key points and provide a navigational chart to help you decide if AWS IoT Device Shadows is the treasure you’ve been seeking.
Key Takeaways:
- AWS IoT Device Shadows offer a reliable way to manage and synchronize device states, ensuring consistency even when devices go offline.
- Even without a direct connection, you can interact with devices through their shadows, providing commands and updates that take effect once connectivity is restored.
- Leverage AWS's robust security mechanisms to protect device state information and ensure only authorized entities can access or modify it.
- While AWS IoT Device Shadows provide a scalable solution, they also introduce an additional layer of complexity that needs careful management.
Decision Framework
When contemplating whether AWS IoT Device Shadows is the right choice for your project, run through this checklist to guide your decision:
- Do you need a reliable way to maintain device state consistency across disconnections and network interruptions?
- Is the ability to interact with and send commands to devices, even offline, crucial for your application?
- Is security a top priority, requiring robust mechanisms to protect device state and interactions?
- Are you managing a large fleet of devices and need a scalable solution but are also mindful of the added complexity?
- Are you conscious of resource utilization and associated costs?
- Does your application require real-time interaction with devices?
Our Team as Your AWS IoT Solutions Partner
Team Serverless is not just proficient; we are passionate about transforming your IoT visions into reality, ensuring every step of the way is paved with best practices, robust security, and scalable solutions.
Drawing from our vast reservoir of experience, we’ve navigated through diverse IoT challenges, emerging not just unscathed but triumphant. Our journey with AWS IoT Device Shadows has honed our skills to the point where we can confidently say, "We've got this!"
In our collaboration with Milnorway, a trailblazer in smart climate control appliances, we delved deep into the intricacies of their expansive IoT network. Our mission? To ensure every node, every device, and every shadow was functioning and optimized to perfection. By rigorously applying AWS IoT best practices, especially in terms of security, we transformed their system into a fortress of reliability and resilience. The result? A network that performs seamlessly and stands tall against threats, ensuring a harmonious balance of performance and protection.
Our commitment doesn't hit pause at implementation. Oh no, we're in it for the long haul! We prioritize empowering your team and transferring our knowledge and expertise to ensure they are more than just users—they are masters of their IoT domain. From managing and scaling to enhancing security, we guide you through seamlessly integrating AWS IoT best practices into your everyday operations. If you're seriously set on bringing your IoT project to life, call us. Also, don't forget to check these AWS IoT use cases and examples.
Wrapping Up
Understanding and effectively implementing AWS IoT Device Shadows is crucial for maintaining a robust and scalable device network. IoT Device Shadows play a pivotal role in modern IoT architectures, from ensuring consistent device state management to enabling offline interactions and enhancing security.
Throughout this article, we've explored the ins and outs of IoT Device Shadows, covering their advantages and potential drawbacks and providing practical advice on implementation. We've also delved into real-world scenarios, helping you understand the contexts in which IoT Device Shadows genuinely shine.
As we wrap up this comprehensive guide, it's clear that the journey to mastering AWS IoT Device Shadows is intricate but incredibly rewarding. And you don't have to walk this path alone. Our serverless consultion experts are at the ready, armed with knowledge, experience, and a genuine passion for IoT innovation.